 https://eb-advisorygroup.org/wp-content/uploads/2023/09/1-Basketball-means-the-world-2.png
480
605
Cem Karamursel
https://eb-advisorygroup.org/wp-content/uploads/2021/05/europead-basketball-advisory-group-logo.png
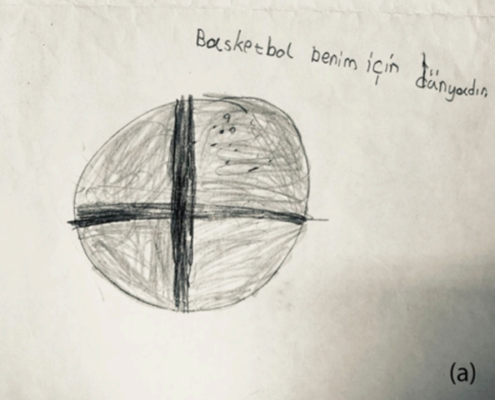
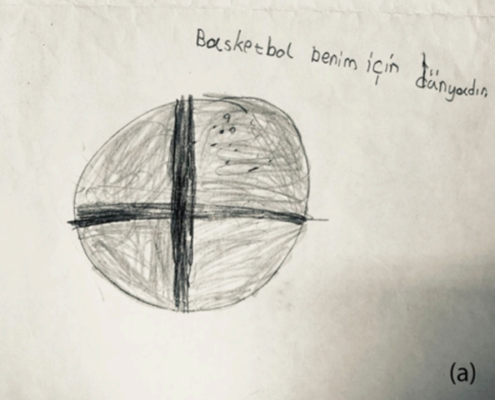
Cem Karamursel2023-09-03 15:25:142023-09-03 15:53:34Children’s Perceptions of Basketball*…
https://eb-advisorygroup.org/wp-content/uploads/2023/09/1-Basketball-means-the-world-2.png
480
605
Cem Karamursel
https://eb-advisorygroup.org/wp-content/uploads/2021/05/europead-basketball-advisory-group-logo.png
Cem Karamursel2023-09-03 15:25:142023-09-03 15:53:34Children’s Perceptions of Basketball*…
CREATING NEW IDEAS FOR EUROPEAN BASKETBALL
European Basketball Advisory Group (EBAG) is a non-profit network of independent individuals who have a great passion for basketball and do care about increasing its popularity, especially among kids and teenagers.
DETAIL INFO
We are looking forward to getting in touch with you
Share your comments or questions with us. Let us know in case you are interested in obtaining more information about our areas of focus, projects or reports.
BLOG
 https://eb-advisorygroup.org/wp-content/uploads/2023/09/1-Basketball-means-the-world-2.png
480
605
Cem Karamursel
https://eb-advisorygroup.org/wp-content/uploads/2021/05/europead-basketball-advisory-group-logo.png
Cem Karamursel2023-09-03 15:25:142023-09-03 15:53:34Children’s Perceptions of Basketball*…
https://eb-advisorygroup.org/wp-content/uploads/2023/09/1-Basketball-means-the-world-2.png
480
605
Cem Karamursel
https://eb-advisorygroup.org/wp-content/uploads/2021/05/europead-basketball-advisory-group-logo.png
Cem Karamursel2023-09-03 15:25:142023-09-03 15:53:34Children’s Perceptions of Basketball*…
Resilience is the key for overcoming crises… But how resilient is the European Basketball?
Resilience is the key for overcoming crises… But how resilient is the European Basketball? A detailed look at some major crises in the past and how European Basketball reacted

Coronavirus outbreak – A huge catastrophe for European basketball or an opportunity to start thinking differently?
Coronavirus outbreak – A huge catastrophe for European basketball or an opportunity to start thinking differently?
